Welcome to a New Era of Cybersecurity Risk Management
As the nature of our work undergoes profound changes, and everything is connected, it brings forth a shifting landscape of cyber threats. Yokogawa recognizes the importance of ensuring the safety and security of our customers' industrial operations. Therefore, we offer a comprehensive range of cybersecurity solutions and services that are rooted in sound risk management strategy.
Our approach revolves around providing long-term lifecycle services specifically suited to our customers' unique challenges. With an unwavering commitment to minimizing risks, Yokogawa acts as a dedicated lifecycle valued partner. Our ultimate goal is to become your foremost ally, fostering enduring, stable, and secure operations across your plant, and across your enterprise.
Yokogawa is seeing customer's plants as important as a human body.
Yes, I Want a Consultation
-
Secured Remote Solutions
Secured and controlled access to critical, actionable data at any time and from anywhere.
-
Cybersecurity Lifecycle Management
- Yokogawa’s cybersecurity services
- Cybersecurity lifecycle management
- Control security risks
- Highest business continuity plan throughout plant lifecycle
-
Cybersecurity Consulting Services
Yokogawa’s comprehensive Cybersecurity Consulting Services help customers deploy proper security solutions for their plants to ensure safe operation while adapting to new technology for achieving higher efficiency and productivity.
-
Product Security
Yokogawa has established the basic policy and measures criteria for the security control of products.
-
OpreX IT/OT Security Operations Center (SOC)
Managed IT/OT cybersecurity services for threat detection and remediation
Resources
Rousselot Ghent won Belgium Factory of the Future Award. Yokogawa has supported Rousselot with automation systems since 1993.
Data of 20,000 tags gathered by Exaquantum helped to find the ideal production parameters.
A virtual network system that securely connects OT-IT built on existing network resources.
Yokogawa experts monitor the network remotely like customer's information system department.
At the 2015 ARC Industry Forum in Orlando, Florida in February, Yokogawa announced a collaboration with Cisco to deliver Shell’s SecurePlant initiative, a comprehensive security management solution for plant control systems jointly developed by Cisco, Yokogawa, and Shell. This report explains how Cisco Systems and Yokogawa worked with Shell to co-develop the company’s “SecurePlant” cybersecurity solution for its control systems.
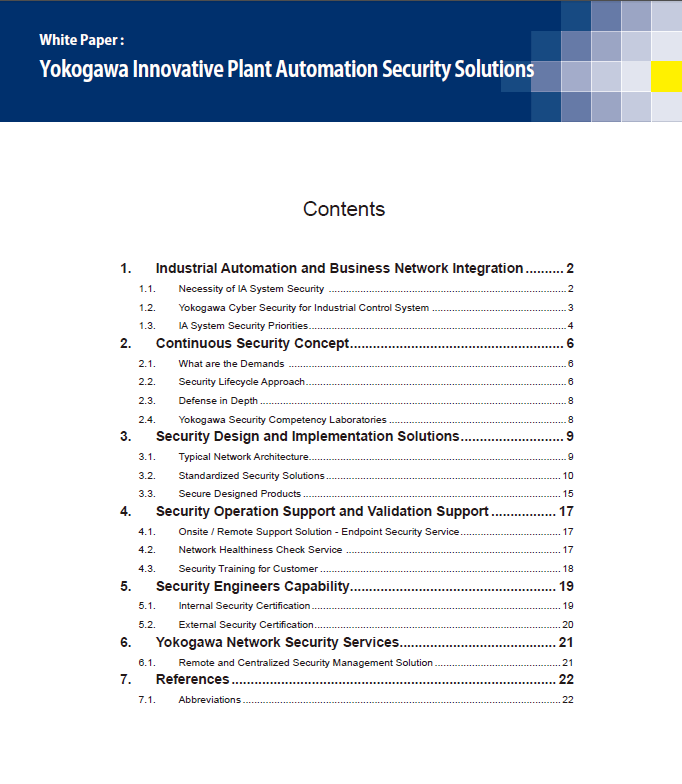
Network and system security is now a necessity in process automation industry. YOKOGAWA provides a service lifecycle solution for cyber security to ensure that the security measures and deployments are continuously enhanced, monitored and inspected.
This white paper explains the details of the security design, implementation, operation and validation solutions from the technical perspective.
Mitigation strategies for cybersecurity risks in the hydrogen ecosystem include implementing network security measures such as segmentation and isolation of ICS networks, intrusion detection and prevention systems, and access controls. Endpoint protection is crucial to secure devices connected to the network from malware and other unauthorized applications.
The agnostic approach to cybersecurity and solution integration, built around the concept of modularity, offers a scalable and flexible way to reduce the risk of cyberattacks on OT networks.
Watch for a backdoor cyber security assualt. The Juniper Networks incident in December 2015 changed how industry looks at device security as hackers exploit deliberate weaknesses being installed into software. End users, integrators, and device manufacturers need to adapt and prepare for this new reality. Follow these cyber security steps.
Supervisory control and data acquisition (SCADA) systems have been part of the process industries for many decades and cyber security measures need to grow as technology advances. SCADA systems are used in oil and gas pipeline and other remote control and monitoring applications, such as electrical transmission and distribution, and water/wastewater.
While cyberattacks and countermeasures are likely to evolve forever, there’s no reason the trip can’t prove successful and satisfying.
For more YNOW2024 articles, please visit YNOW: A Yokogawa Users Conference | Control Global
When it comes to digital transformation, Petronas’ Sharul Rashid wants to see more collaborative efforts.
For more YNOW2024 articles, please visit YNOW: A Yokogawa Users Conference | Control Global
Downloads
Brochures
Videos
Yokogawa's Sustainable IT OT Cybersecurity Services, protects your industrial IT/OT network from malicious actors and code.
Discover how to achieve industrial autonomy step by step through one of the 75+ inspiring presentations.
This workshop provided by industry partners Yokogawa and ThreatConnect will show you a way to strategically manage cyber risk within an industrial environment. Learn how to transition from the “break/fix” model of industrial cybersecurity to a business risk management strategy through cyber risk quantification, return on investment (ROI) for industrial cybersecurity solutions calculations, and cyber risk identification.
With the new Industrial Network standards like ISA-IEC62443 companies are evolving their IT and OT networks to face evolving threats. This presentation will cover industrial networking best practices, secure architectures and segregation techniques that can be used by all businesses to prevent a minor business network breach from becoming an industrial catastrophe.
In our first episode, Tom Hardy debunks common false statements regarding Cybersecurity. Does insurance liability protect businesses against cyberattacks? Is my organization too small to be a target? Tune in to find out.
News
-
Press Release May 8, 2015 Yokogawa Promotes GICSP Training to Enhance Plant Safety
Looking for more information on our people, technology and solutions?
Contact Us